SSRS won’t bind HTTPS to new certificate — “We are unable to create the certificate binding”
This blog post is around the situation where you have SSRS setup to use HTTPS and thus using a certificate and the certificate expires (or just needs replacing). We had caught the initial error via our Continuous Monitoring of the SSRS site — basically when the certificate expired we got an exception and alerted on it.
The client installed a new certificate but the issue arose where in Reporting Service Configuration Manager we went to use the new certificate but when we chose it we got this error:
“We are unable to create the certificate binding”
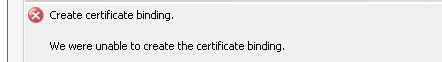
And Reporting Service Configuration Manager removes the HTTPS binding.
We checked and the certificate is installed correctly.
So we looked in SSRS logs:
C:Program FilesMicrosoft SQL ServerMSRS11.<instance>Reporting ServicesLogFiles
It is amazing for a reporting system how badly errors are reported in the log files. Basically there was nothing in there at all:
rshost!rshost!964!12/11/2017-08:13:47:: e ERROR: WriteCallback(): failed to write in write callback. rshost!rshost!2aa4!12/11/2017-08:13:47:: e ERROR: Failed with win32 error 0x03E3, pipeline=0x00000002780A7D80. httpruntime!ReportServer_0-33!2aa4!12/11/2017-08:13:47:: e ERROR: Failed in BaseWorkerRequest::SendHttpResponse(bool), exception=System.Runtime.InteropServices.COMException (0x800703E3): The I/O operation has been aborted because of either a thread exit or an application request. (Exception from HRESULT: 0x800703E3) at Microsoft.ReportingServices.HostingInterfaces.IRsHttpPipeline.SendResponse(Void* response, Boolean finalWrite, Boolean closeConn) at ReportingServicesHttpRuntime.BaseWorkerRequest.SendHttpResponse(Boolean finalFlush) library!ReportServer_0-33!2aa4!12/11/2017-08:13:47:: e — End of inner exception stack trace —;
We knew that HTTP was working all good so SSRS itself was “ok”. So on a hunch we decided to see if the old certificate was still lying around bound to something and so using netsh:

So we then removed the binding — which was safe enough as only SSRS was serving web requests on this server — IIS was not being used at all.:
netsh http delete sslcert ipport=[::]:443

We could then bind the new certificate in Reporting Service Configuration Manager:

So hopefully if you get this type of error you too can solve it nice and quickly and have your web service URL and Report Manager URL nice and secure again…
