Security Events & Alert Management
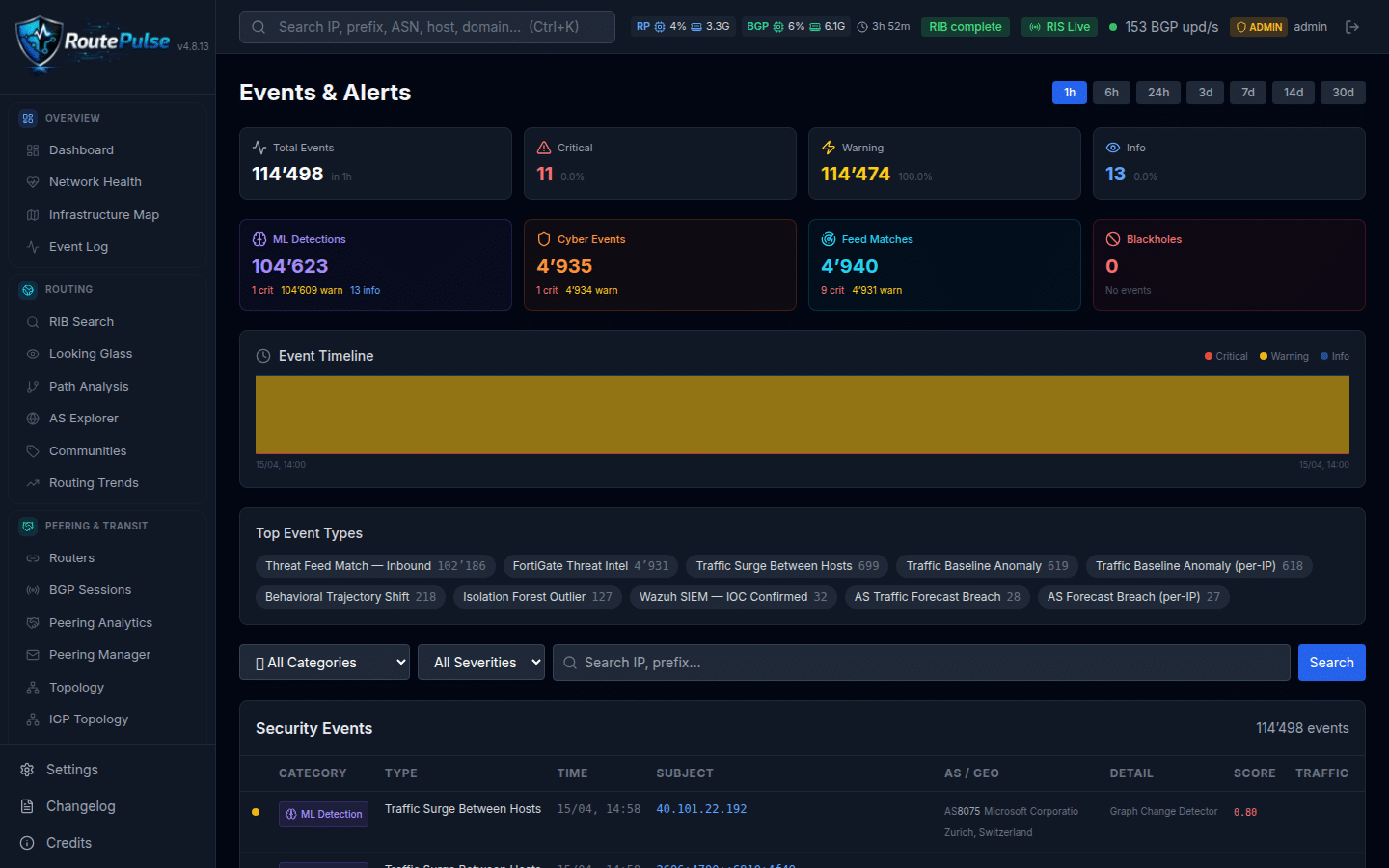
RoutePulse provides a unified event timeline that combines ML-based detections, cyber events, threat feed matches, BGP anomalies, mitigations, and infrastructure events into a single operational view. The platform handles 47 notification types organized across 8 categories: Infrastructure (4 types), BGP Routing Anomalies (19 types), CyberSecurity (8 types), Threat Intelligence (6 types), ML Engine (1 type), ANIE Autonomous Intelligence (2 types), AI Insights (5 types), and Mitigation (2 types). Over 45 human-readable event type labels translate internal identifiers into clear descriptions — for example, cyber_cusum_shift becomes “CUSUM Shift Detection” — ensuring that every alert is immediately understandable by SOC analysts without requiring knowledge of internal naming conventions.
Three delivery channels ensure alerts reach the right people: Telegram with HTML-formatted messages rate-limited at 20 messages per 60 seconds, Email using GOLINE branded templates, and Webhooks delivering JSON POST payloads with ready-made recipes for Slack, Discord, PagerDuty, and Jira. Severity filtering uses color-coded badges for CRITICAL, WARNING, and INFO levels, and all detection types include MITRE ATT&CK mapping. A configurable 7-minute startup grace period (adjustable from 1 to 30 minutes) suppresses notifications during RIB dump ingestion, RPKI load, and ML baseline convergence. The own-AS severity gate ensures that events involving AS202032 or announced prefixes are escalated to CRITICAL. Per-anomaly-type rate limiting caps at 20 per hour globally, with per-IP plus type cooldown for threat intelligence events set at 1 hour. Expandable detail rows reveal full host enrichment context including IP, ASN, country, threat score, abuse score, and ensemble confidence. A time range selector spans from 1 hour to 30 days, and a WebSocket live event feed enables real-time monitoring without page refresh.
Key Capabilities
- Unified event timeline combining ML detections, cyber events, threat feeds, BGP anomalies, mitigations, and infrastructure events
- 47 notification types across 8 categories covering the full spectrum of network and security events
- 45+ human-readable event type labels translating internal identifiers into clear analyst-friendly descriptions
- 3 delivery channels: Telegram (HTML-formatted, rate-limited), Email (GOLINE branded), and Webhooks (Slack/Discord/PagerDuty/Jira recipes)
- Severity filtering with color-coded CRITICAL, WARNING, and INFO badges
- MITRE ATT&CK mapping for all detection types to align with industry threat frameworks
- Configurable startup grace period (1-30 min, default 7 min) suppressing alerts during RIB dump, RPKI load, and ML convergence
- Own-AS severity gate escalating events involving AS202032 or announced prefixes to CRITICAL
- Per-anomaly-type rate limiting at 20/hr globally with per-IP+type cooldown for threat intelligence (1h)
- Expandable detail rows with full host enrichment: IP, ASN, country, threat score, abuse score, ensemble confidence
- Time range selector from 1 hour to 30 days for flexible event investigation
- WebSocket live event feed for real-time monitoring without page refresh
Engineered and operated by the GOLINE SOC & Network Engineering team.
Explore all RoutePulse features →